Nestle Canada Inc. is recalling certain Gerber brand baby cereals due to Cronobacter contamination. The Canadian Food Inspection Agency (CFIA) discovered this contamination in the Oat Banana & Mango Baby Cereal, prompting the recall notice issued today.
The contaminated cereal was distributed in 227-gram containers across several provinces, including Alberta, British Columbia, Manitoba, New Brunswick, Ontario, Quebec, and Saskatchewan. It is also possible that the cereal reached other provinces and territories.
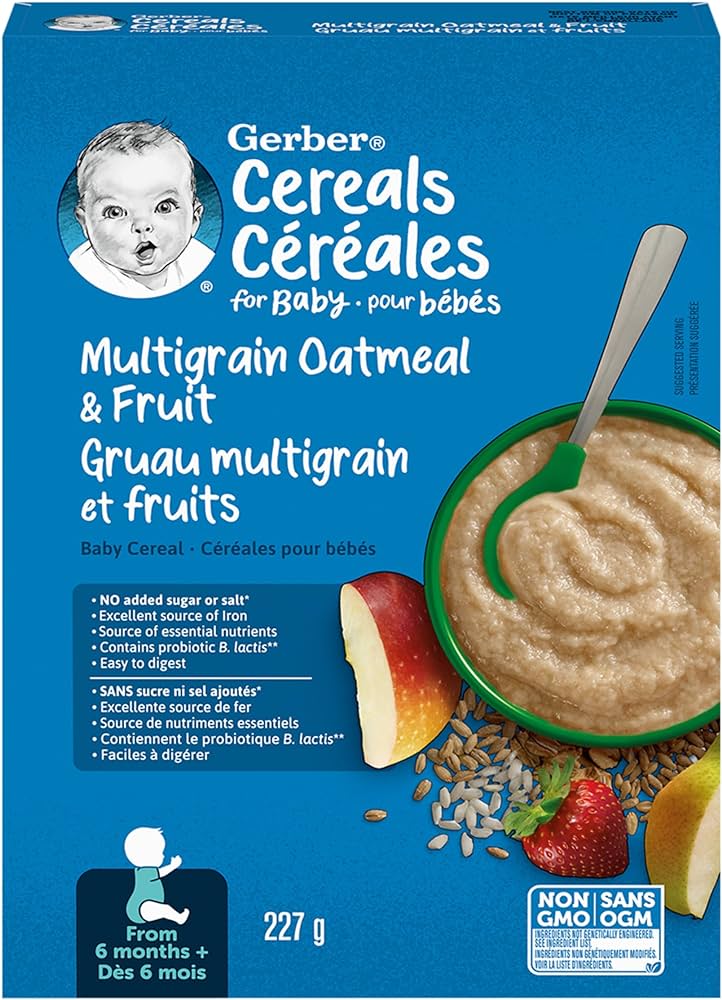
The recall affects products marked with the UPC number 0 65000 13361 5 and the code 2025 MA 30 3334007809. The recall notice did not provide any images of the product. Currently, there have been no reported illnesses related to this contamination.
Consumers are urged to inspect their homes for the affected cereal and discontinue use immediately, as Cronobacter infections can be severe. The CFIA is conducting an investigation into the food safety issue and is ensuring that all recalled products are being removed from store shelves.